
- …
- …

Why Do Enterprises Need DAM+?
Traditional DAM solutions have long supported compliance requirements, today’s security landscape demands more.
With stricter regulations, expanding application environments, and rapidly growing audit data, enterprises need a next-generation approach that can support real-time monitoring, scalability, and evolving security policies—driving the need for DAM+.

What Our Customers Ask?
- Can DAM support cost-efficient high availability with Active-Active architecture?
- How can I find out if the data access volume of the company's subsidiaries in various locations is abnormal?
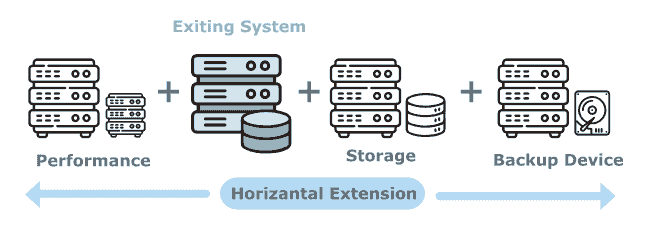
- Operational growth has led to increasingly larger database access volumes, and the existing DAM hardware resources, performance, and storage are severely insufficient. How can this be extended?
- The company has adjusted its database operating system brand restriction policy. Can DAM support switching to a different operating system?

dataisec DAM+
Data leakage remains a common security challenge. By monitoring how applications access databases and identifying abnormal behavior in real time, organizations can reduce breach risks.
Dataisec DAM+ applies advanced database activity monitoring technologies to analyze database operations and system traffic, delivering greater visibility and control over data usage.
DAM+ Delivers Unlimited Scalability Without System Constraints
Dataisec DAM+ is a next-generation database activity monitoring system that supports leading database platforms and delivers scalable, resource-efficient architecture. With complete access traceability and intuitive dashboards for detecting abnormal behavior, DAM+ enables rapid incident investigation and has become an essential security tool for safeguarding enterprise data assets.
Innovative Architecture
- A distributed deployment architecture combining a central security platform with containerized services, enabling unlimited horizontal scalability without system performance constraints
- Active-Active high availability architecture with automatic service recovery, ensuring uninterrupted monitoring and no loss of audit records
- Flexible deployment across on-premises, cloud, or hybrid cloud environments, supporting diverse enterprise IT strategies
- Platform operations independent of application vendor constraints, allowing seamless integration across heterogeneous systems
- Built-in load balancing architecture, delivering optimal cost efficiency and security effectiveness for large-scale audit data management
- Dynamic resource load balancing mechanisms, ensuring efficient resource utilization without waste
Key Features
1It can accurately identify application users or their groups, link database access behavior, and is the best tool for rapid tracing; it can also define application user groups and formulate alarm policies for branch offices, branches or multi-shift systems..
2Monitor the complete access path from the application to the database, retain access records of sensitive data being stolen, altered, damaged, lost or leaked, and ensure compliance standards.
3Delivers highly customizable dashboards and reports for different roles, enabling organizations to gain comprehensive, real-time insight into system status.
4Offers dedicated compliance and security audit dashboards tailored for enterprise regulatory needs, helping organizations meet industry and regulatory requirements.
5Leverages machine learning technologies to identify abnormal behavior, significantly enhancing overall data security.
6Automatically determine optimal alert thresholds based on behavior patterns, reducing false positives and eliminating false alerts.
7Support multi-level approval workflows to streamline incident notification and escalation.
8Provides continuous analysis of anomalies and risk trends, enabling organizations to improve security posture over time.
9Monitors system resource usage and service health in real time, issuing alerts to ensure stability and service quality.
10Enable sensitive data and log masking to protect confidential information and prevent data leakage.
11Support centralized management of logs from various log management tools, consolidating records, activity trails, and evidence with a unified interface for analysis, reporting, and administration.
12Integrates application security scanning tools to correlate vulnerability risks with database access audit records, supporting vulnerability remediation prioritization and delivering continuous improvement reports and dashboards.
Dataisec Technologies Inc.
Tel: +886-2-8771-3878
Fax: +886-2-8771-3790
3F., No. 7, Ln. 116, Guangfu S. Rd., Da’an Dist., Taipei City, Taiwan, (R.O.C.)
@ 2026 Dataisec Technology Inc. All Rights Reserved




