- …
- …
Application User Tracking
Importance & Use Cases

Comprehensive Auditing of AP-to-DB Access Activities
Audits database access activities initiated by application users (AP Users), enabling organizations to trace database interactions back to real users and meet regulatory compliance requirements.

Monitoring Anomalous Behavior Across AP User Groups
Group AP users with similar business roles and apply group-based security policies to detect and contain risks at the earliest stage of suspicious behavior.

Mitigate penalties resulting from data breaches
In the event of sensitive or personal data leakage, failure to identify the responsible party due to insufficient evidence may prevent the mitigation of regulatory penalties.
Driven by years of technical innovation, dataisec developed the Application User Tracking Module (APU) to deliver true user-level visibility and accountability for database security.
The Application User Tracking Module (APU) enables precise tracking of application users (AP Users) without requiring any modifications to existing applications. By complementing the limitations of traditional DAM solutions, APU delivers comprehensive database access traceability across the five key dimensions—who, what, when, where, and how.
APU supports a wide range of application server architectures and deployment models, including the following scenarios:
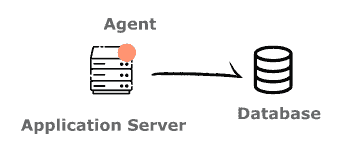
1. Single Application Server Accessing Databases
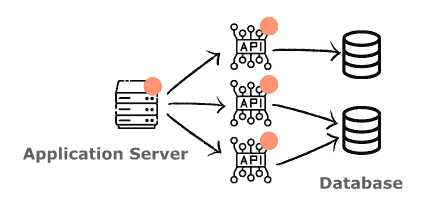
2. Distributed Systems / Microservices Accessing Databases
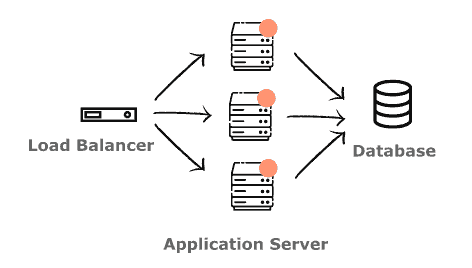
3. Load-Balanced Application Server Clusters Accessing Databases
Dataisec Application User Tracking Module (APU) supports leading application server platforms and seamlessly integrates with the next-generation Database Activity Monitoring system (DAM+).
Together, they deliver comprehensive database access monitoring and security auditing—ensuring true compliance while maximizing cost efficiency for enterprises.
Dataisec Technologies Inc.
Tel: +886-2-8771-3878
Fax: +886-2-8771-3790
3F., No. 7, Ln. 116, Guangfu S. Rd., Da’an Dist., Taipei City, Taiwan, (R.O.C.)
@ 2026 Dataisec Technology Inc. All Rights Reserved